KYT & Transaction Monitoring
Real-Time Transaction Monitoring for Lifecycle Risk Management
Monitor transactions in real time, detect suspicious behavior early, trigger AML case workflows automatically, and give compliance teams the tools to investigate, review, and act with confidence.
Problem
Why Transaction Monitoring matters
Onboarding Is not enough
Customer verification at signup is only the beginning. Risk can appear later through transaction behavior.
Suspicious activity needs fast action
Unusual transfers, changing patterns, and risky behavior need to be detected early.
Manual review does not scale
As transaction volumes grow, compliance teams need automation and clear workflows to keep up.
Stronger monitoring means stronger compliance
Good transaction monitoring helps teams detect risk, investigate alerts, and maintain better AML control.
One modular platform
Unified Trust and Compliance Across the Full Customer Lifecycle
Most companies use separate tools for identity verification, AML screening, transaction monitoring, and case management. Identomat brings all of it together so signals do not get lost, decisions happen faster, and compliance becomes operational instead of reactive.
IDV
Identity document verification
KYC
Know your customer & business
AML Screening
Sanctions, PEP, Adverse media
Transaction Monitoring
Real-time KYT & Behavioral analysis
Case Management
Alert Triage & Investigation
Reporting
SAR/STR Generation & Audit trail
Workflow
A clearer way to monitor, detect, and review risk
See how Identomat monitors transaction activity, applies risk logic, generates alerts, and helps compliance teams investigate suspicious behavior faster.
Step 1
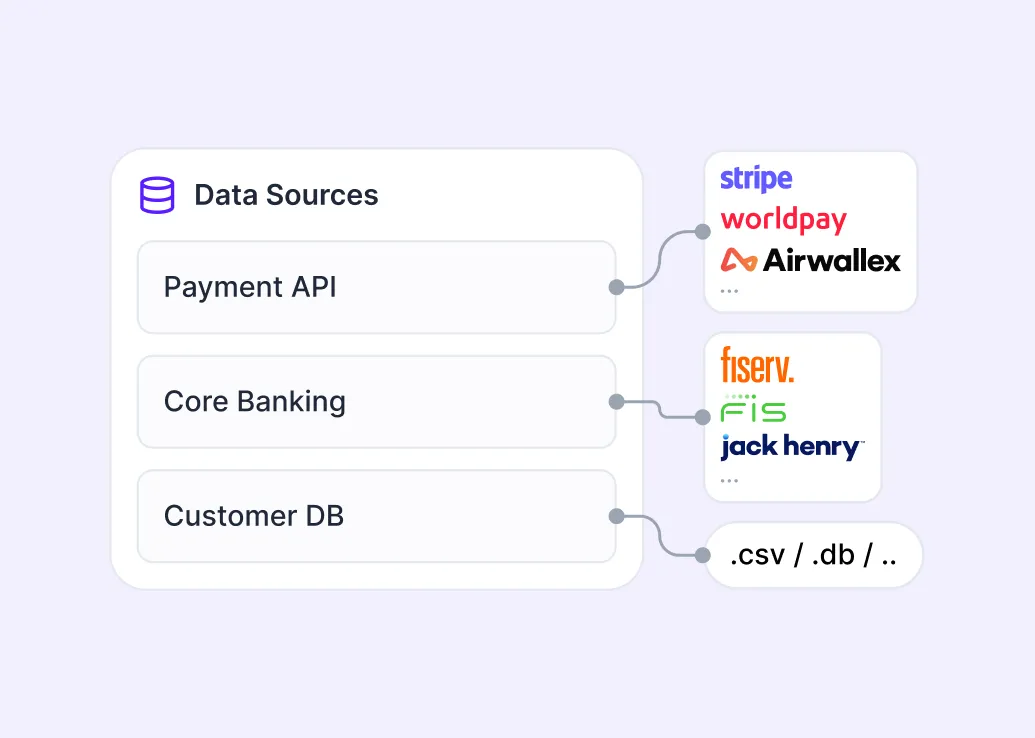
Ingest transaction and customer data
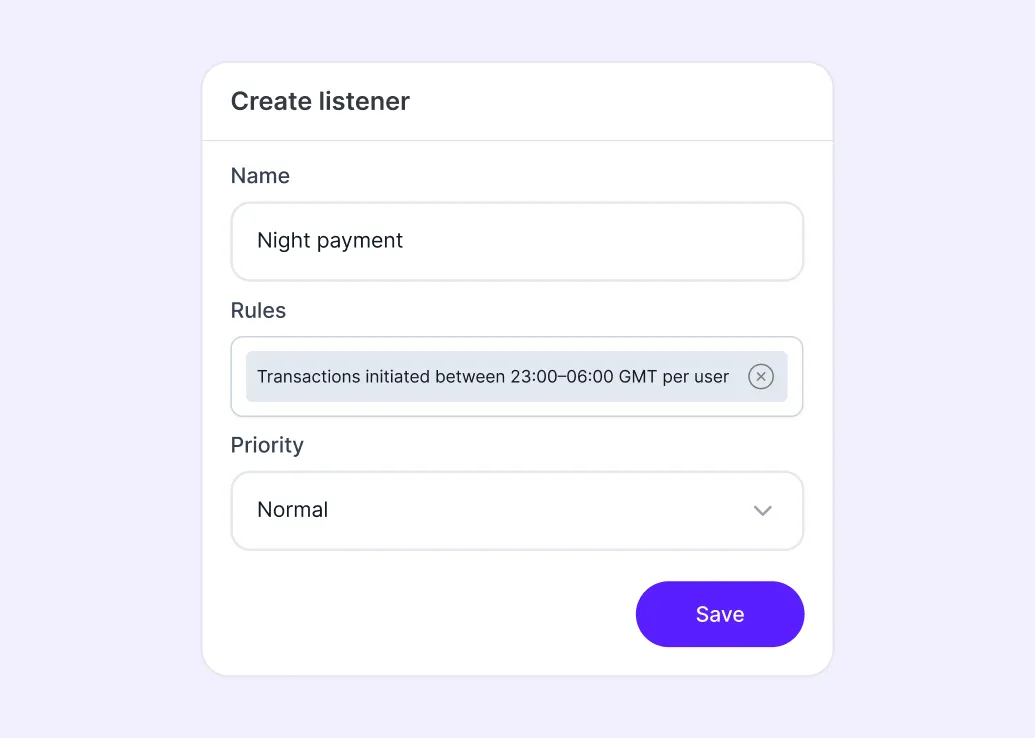
Transaction data enters the system through integrations and mapped fields. Businesses can configure how transaction data is structured and how monitoring actions should be triggered.
Step 2
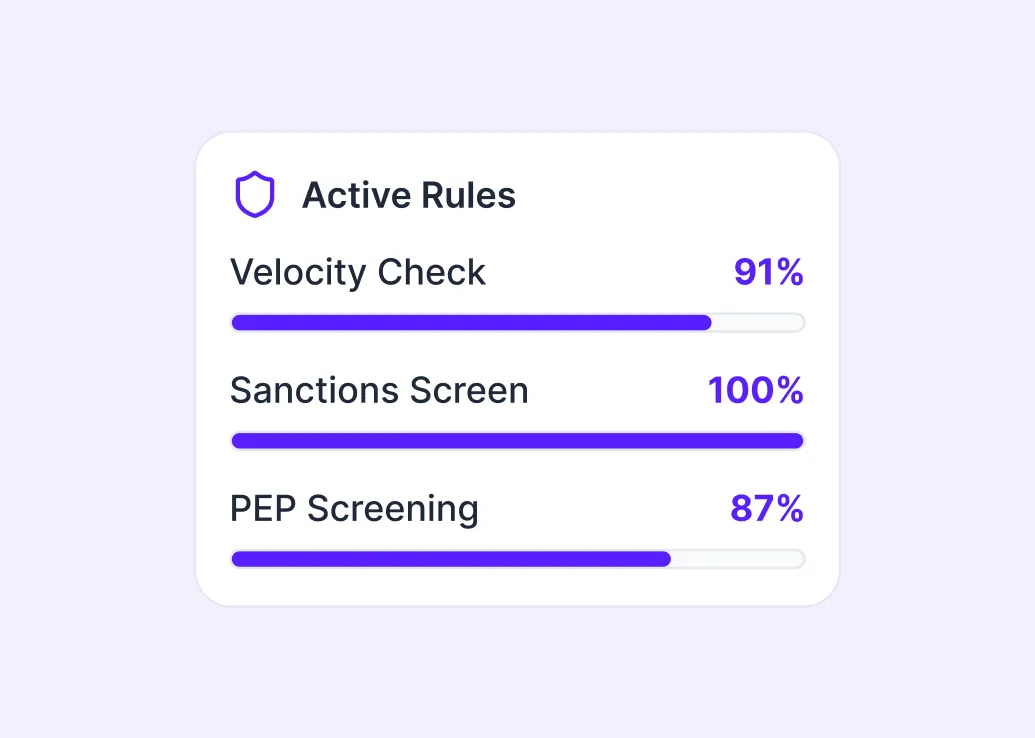
Apply rules, risk logic, and screening
Transactions are evaluated using configurable rules, risk logic, formulas, and AML screening to detect suspicious activity.
Step 3
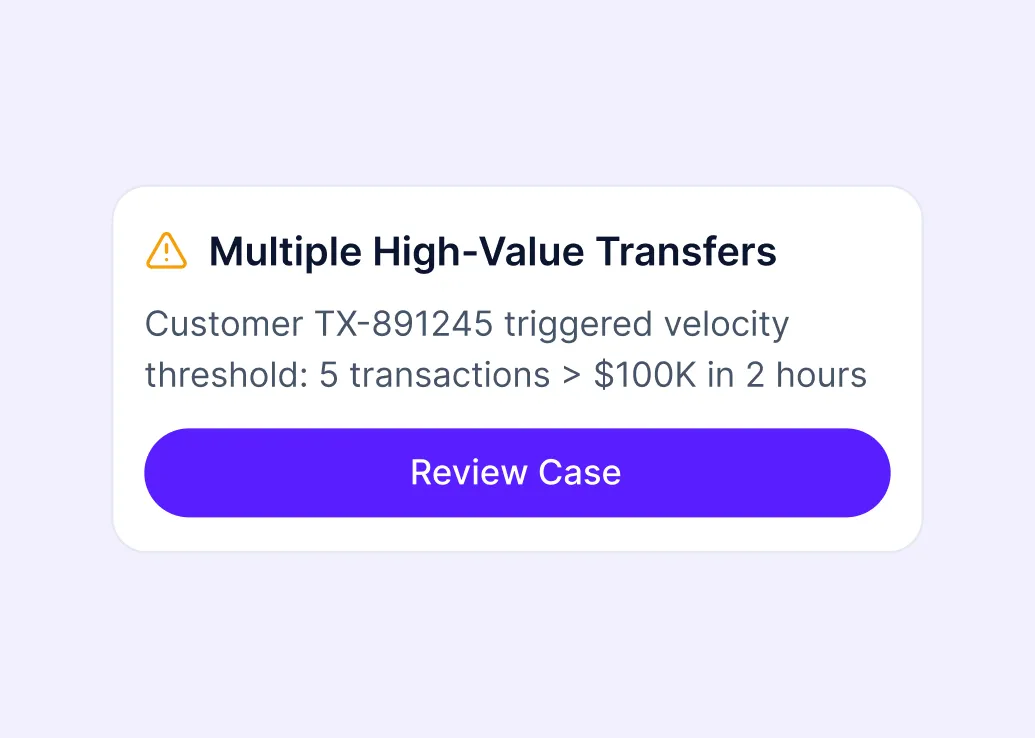
Generate alerts and assign statuses
When suspicious patterns or screening hits are detected, the system creates alerts and assigns statuses such as accepted, rejected, under review, AML hold, or hold for manual review.
Step 4
Review and investigate cases
Compliance teams can review flagged transactions, open AML cases, examine supporting data, assess results, and document actions taken. They can also resolve and track false positives.
Step 5
Report, refine, monitor continuously
Teams can generate reports, review alerts, refine thresholds, adjust rules, and improve performance over time. Ongoing monitoring is a key part of a modern AML and KYT setup.
Key features of Identomat’s Transaction Monitoring
Identomat Transaction Monitoring is a KYT solution that helps businesses monitor transaction activity, detect suspicious behavior, and support faster AML decision-making.
Monitors transaction activity
Track transactions continuously and surface suspicious patterns as they appear.
Detects suspicious behavior
Identify unusual activity based on configured rules, thresholds, and risk logic.
Supports AML investigations
Turn alerts into cases and help compliance teams review and act faster.
Connects risk across workflows
Bring together transaction data, customer context, and case management in one workflow.
Advantages
Where traditional Transaction Monitoring breaks
E-commerce
Monitoring is disconnected from onboarding
Alerts lack customer context
False positives overwhelm analysts
Investigations happen across multiple tools
Decision trails are hard to defend
Identomat Transaction Monitoring
Unified customer and transaction risk view
Real-time screening before transactions are completed
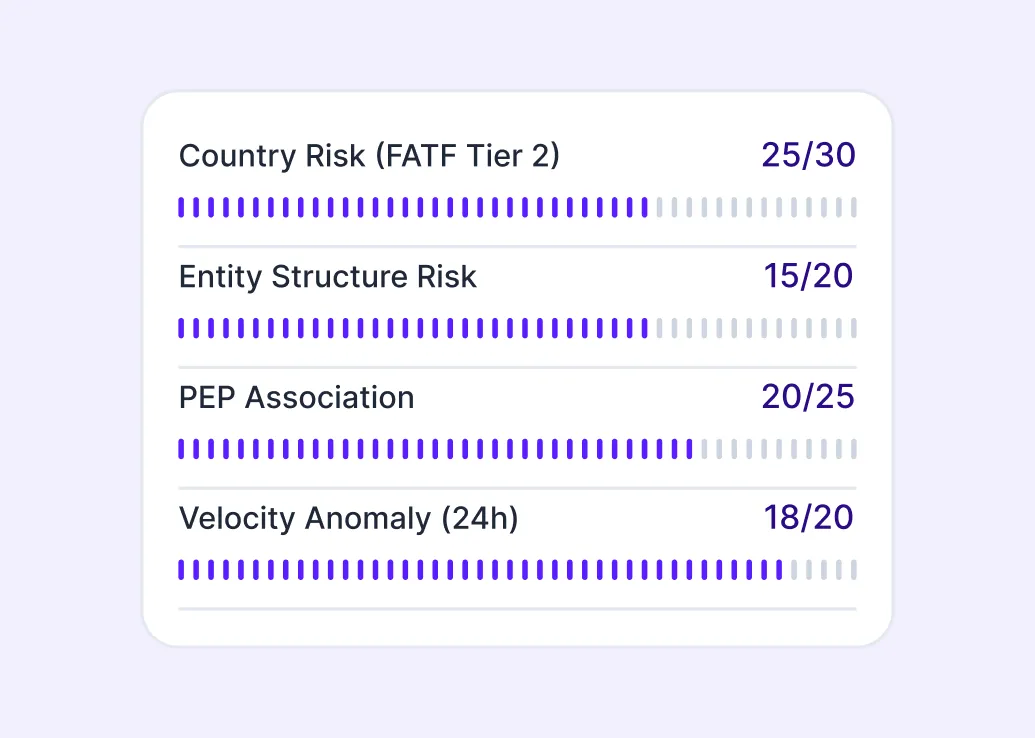
Multi-layer risk scoring across static and dynamic factors
Built-in case management and SAR workflows
Full auditability across the whole lifecycle
Common use cases
KYT across industries
Explore how different industries can use transaction monitoring to detect suspicious activity, strengthen AML controls, and support faster investigations.
Fintech & Payment platforms
Keep up with fast transaction flows, detect suspicious behavior early, and support faster AML reviews. Identomat helps connect transaction monitoring with customer verification, AML Screening, and case workflows in one operational environment.
Banks & EMIs
Build stronger ongoing monitoring around transfers, account activity, and customer risk. Identomat gives teams the tools to detect unusual patterns, trigger alerts, and investigate with greater structure and control.
Crypto exchanges & VASPs
Support KYT processes in high-speed, high-risk environments where transaction visibility matters. Identomat helps combine transaction monitoring with broader KYC and AML workflows for stronger ongoing compliance.
Lending platforms
Spot unusual funding and repayment behavior, surface risk signals earlier, and support better review decisions. Identomat helps lenders connect transaction activity with customer context and AML operations.
Marketplaces & Merchant platforms
Monitor payment activity across multi-user ecosystems and identify patterns that may require review. Identomat helps platforms bring alerts, risk visibility, and investigation workflows into one place.
Investment & Trading platforms
Strengthen oversight of customer transaction behavior and respond faster to suspicious activity. Identomat supports real-time monitoring workflows designed for teams that need clarity, speed, and operational control.
Security & Compliance
Partner you can rely on
Identomat’s solutions are backed by industry-leading certifications, confirming our commitment to the highest security and compliance standards.







FAQ
Frequently asked questions
Everything you need to know about the product and billing.
What does KYT stand for?
KYT stands for Know Your Transaction. In practice, it refers to transaction monitoring used to detect suspicious behavior, support AML controls, and give compliance teams ongoing visibility into customer risk beyond onboarding.
How is transaction monitoring different from transaction screening?
Transaction screening is usually a point-in-time check on a specific payment before it is processed, often against sanctions, watchlists, or blocked entities. Transaction monitoring looks at activity over time to identify patterns, anomalies, and broader behavioral risk that a one-off screen may miss.
What data is typically needed to set up transaction monitoring?
Most transaction monitoring setups start with transaction data plus relevant customer context. On Identomat, the workflow begins by ingesting transaction data through integrations and mapped fields, then connecting that data to risk logic, alerts, customer context, and case workflows.
How can transaction monitoring help reduce false positives?
Strong monitoring setups reduce false positives by using configurable rules, risk-based thresholds, customer context, and continuous tuning instead of rigid one-size-fits-all logic. The goal is to surface genuinely suspicious behavior while cutting unnecessary manual reviews.
What is the difference between rules-based monitoring and behavioral monitoring?
Rules-based monitoring flags predefined scenarios, such as threshold breaches or specific risk triggers. Behavioral monitoring looks for deviations, patterns, and relationships over time. The strongest programs usually combine both approaches so teams can catch obvious risks and more subtle suspicious behavior.
Why is continuous monitoring important even after a transaction initially looks safe?
Because risk can change after the fact. New sanctions, new counterparty intelligence, or newly discovered suspicious patterns can make an earlier transaction look riskier in hindsight. Continuous monitoring helps compliance teams catch those changes and respond before exposure grows.
